In recent years, electronic mail (email for short) has become an essential part of our daily lives. Many people use…
Read moreWhat would you do if your business suffered a ransomware attack tomorrow? Do you have a contingency plan in case…
Read moreIn today’s world, technology is ubiquitous, and connectivity is a must. Securing your home network has become more critical than…
Read moreIt’s a common theme. You begin seeing these amazing CGI images of your friends on Facebook or Instagram. You think,…
Read moreMicrosoft 365 is one of the most popular cloud platforms in the world, with about 345 million paid seats. Microsoft…
Read moreThe need to back up data has been around since floppy disks. Data loss happens due to viruses, hard drive…
Read moreWhether you sell shoes or run an accounting firm, you need some type of technology to operate. Today’s companies aren’t…
Read moreTechnology vulnerabilities are an unfortunate side effect of innovation. When software companies push new updates, there are often weaknesses in…
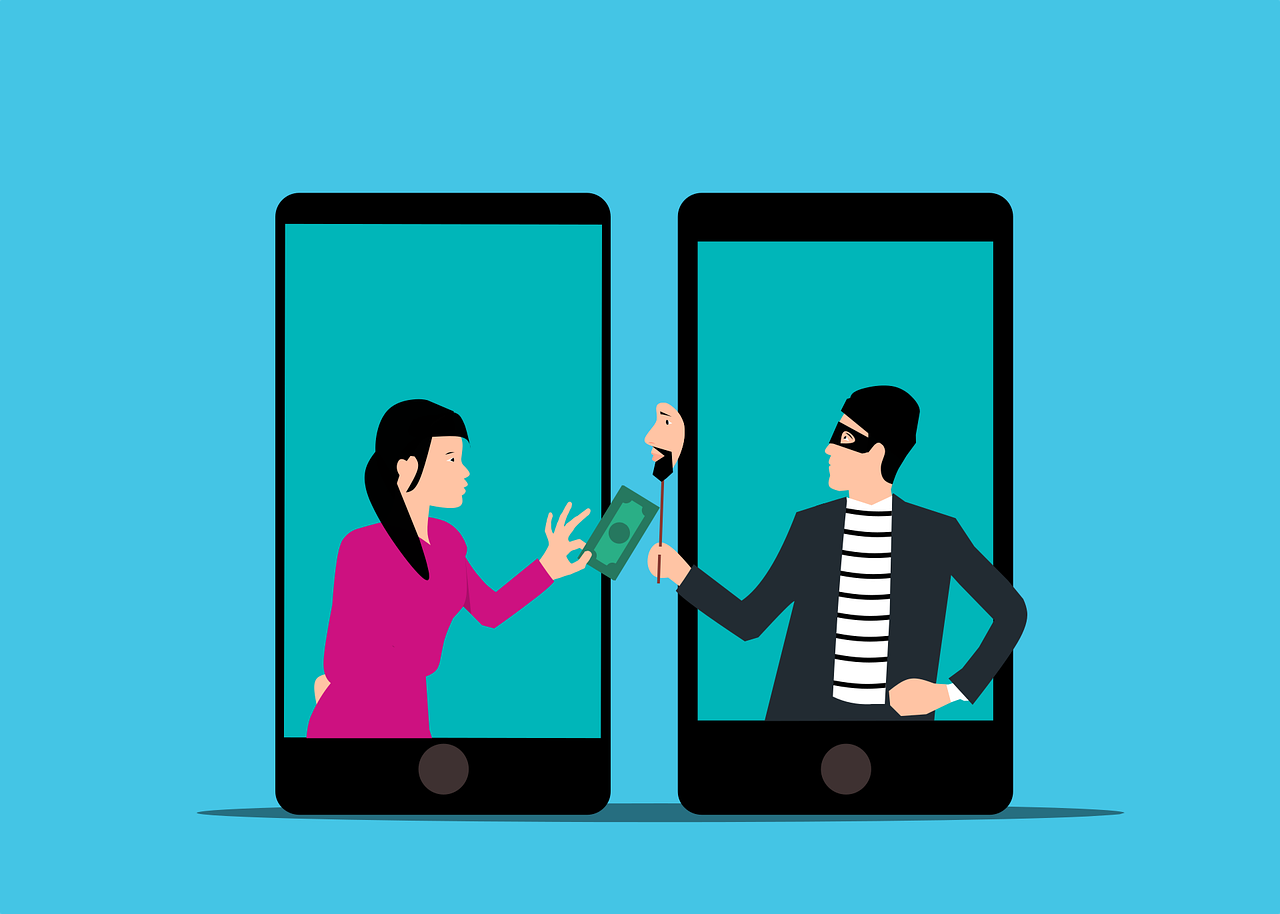
Read moreImagine you’re going about your day when suddenly you receive a text from the CEO. The head of the company…
Read moreBring your own device programs are popular because it’s more affordable than buying a bunch of mobile devices for staff. But employee-owned devices are often a security risk. We’ll tell you how to better manage BYOD to mitigate the chance of a network breach.
Read more









Recent Comments